Authentication
In order for a Partner application to access the Manna APIs, it must be previously registered and duly authorized as a trusted client.
Auth0, an Okta solution
Manna platform relies on Auth0, a leading provider for secure access management, ensuring compliance with GDPR, SOC2, and all industry security standards.
Auth0 is fully integrated with the AWS infrastructure, leveraging IAM to prevent unauthorized access and continuously monitor activity.
The authentication page is hosted by Okta, providing protection against advanced attack techniques.
No passwords are stored on the platform; all accounts are nominal, and two-factor authentication is mandatory by default for all users.
M2M (machine-to-machine) authentication conforms to the OAuth 2.0 standard, as represented in the schema below.
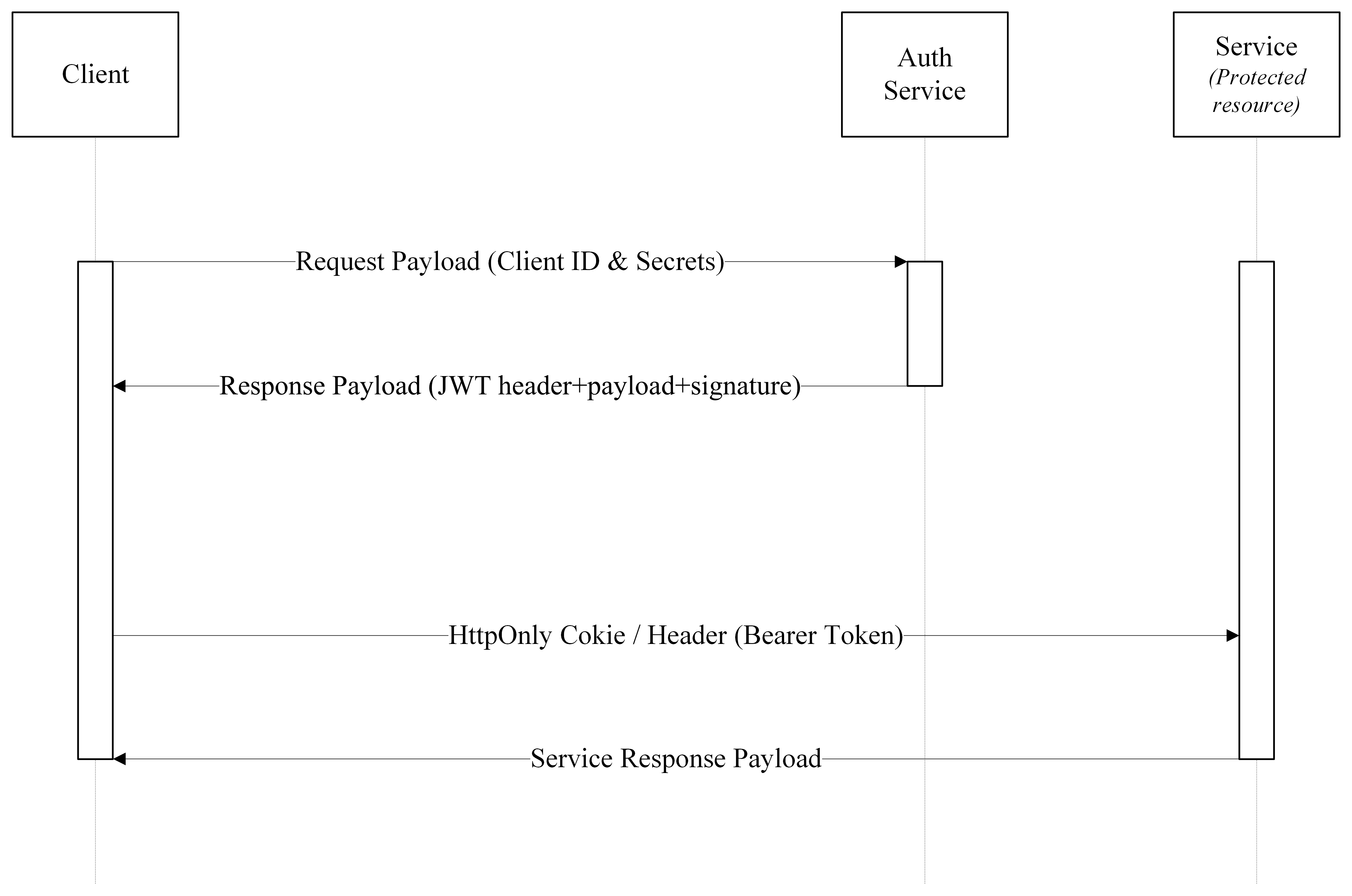
The flow enables Partners to obtain an access token, suitable for enabling access to protected services that is circumscribed, controlled, and temporally limited.
The credentials — Client ID, Client Secret, and Scopes — are issued by the project contact within the framework of the Onboarding procedure.
The credentials permit the univocal identification of the Partner application. Their custody and their use under conditions of security constitute the exclusive responsibility of the Partner; any operation performed by means of such credentials shall therefore be deemed attributable to it.
Once acquired, the application is enabled to request the generation of a JWT (JSON Web Token) at the designated authentication endpoint; such token must be included in each request addressed to the protected APIs, so as to permit access to the relevant resources.
In summary, the process ensures that:
- the identity of the application is verified by means of secure and traceable mechanisms;
- access to the APIs is duly circumscribed, regulated, and subject to control;
- sensitive credentials are in no case exposed directly within the requests.
Application authentication is managed using the native Auth0 SDK – no custom modifications that could introduce vulnerabilities, and continuously updated to ensure security.
The Onboarding contemplates a session with the Networking & Security team, aimed at the verification and validation of technical requirements, the definition of integration modalities, and the identification, under conditions of adequate security, of the clients involved in the process (such as brand legacy systems, technology providers, OMS systems, and additional infrastructural components).
Rate limiting
| Environment | Requests / min | Entities / min |
|---|---|---|
| Dev/Quality | ∞ | ∞ |